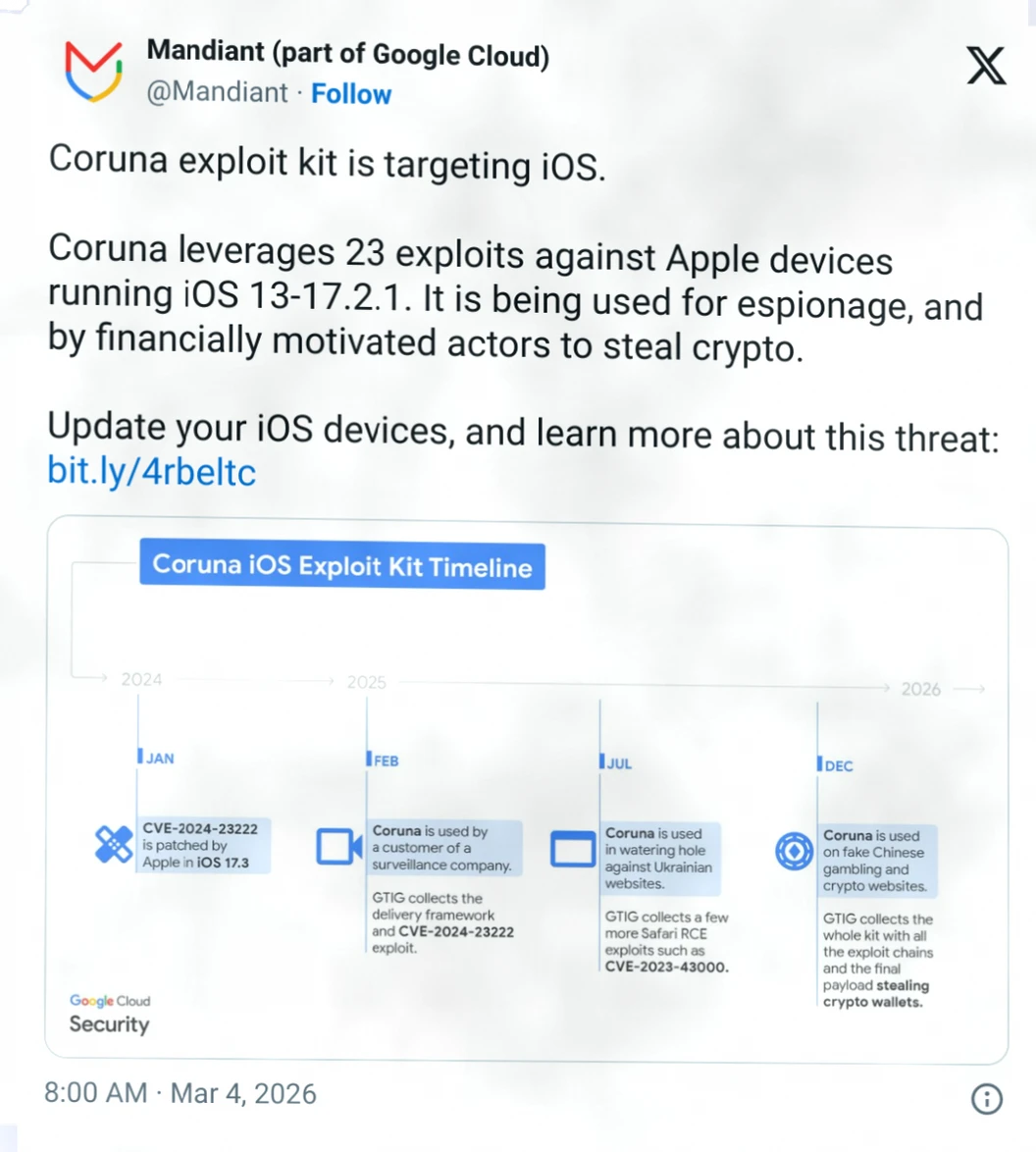
Google's Threat Analysis Group (GTIG) recently revealed an advanced malicious toolkit targeting iPhone users, which specifically steals users' cryptocurrency wallet recovery phrases and sensitive information by spoofing financial websites. Researchers first discovered the JavaScript framework of this toolkit in February 2025, initially used by a client of a monitoring technology company for device fingerprinting to accurately push tailored iOS vulnerability payloads.
Later that year, the framework was found hidden within multiple compromised Ukrainian websites, pushing to iPhone users in specific geographic regions, demonstrating highly targeted attack characteristics. By December, researchers identified the same code on numerous counterfeit Chinese financial websites, including phishing pages impersonating the well-known crypto exchange WEEX.
The toolkit not only identifies the visitor's device but also actively scans for popular crypto applications installed on the device, such as Uniswap and MetaMask, attempting to extract wallet private keys, recovery phrases, and other core credentials to facilitate asset theft.
Rocky Cole, co-founder of security firm iVerify, told WIRED that the development cost of this toolkit is as high as several million dollars, with a high level of technical complexity. Its code structure is highly similar to known cyber weapons supported by the U.S. government. He emphasized that this is the first observation of a module suspected to originate from state-level cyber tools being misused by terrorist organizations, transnational crime groups, and black market forces, marking a systematic lowering of the threshold for cyber attacks.

